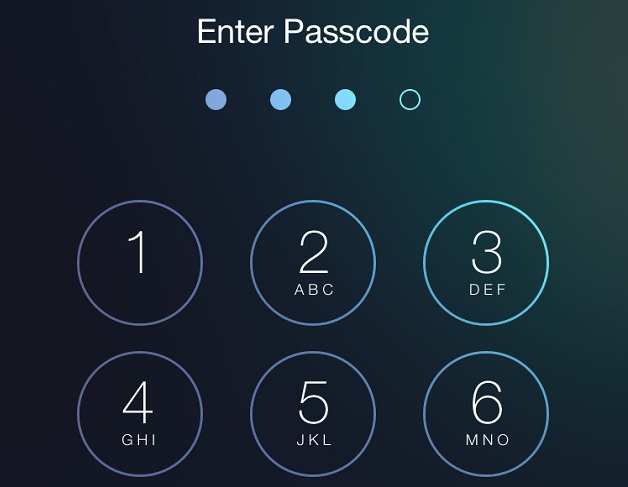
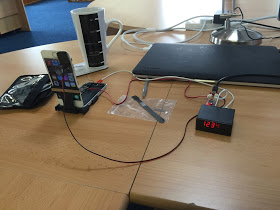
When we think about protecting our iPhone, iPad or iPod touch and data stored in it from intruders the first thing that we do is add a 4-digit passcode to our device. Now it seems like this measure is insufficient as hackers have figured out a way to unlock an iOS device by bruteforcing the lockscreen. For this they have developed a special device called the IP Box. This device was put to test by MDSec, who were able to get access to this it at a price of £200 (or around $300).
The physical device connects with the iPhone with a USB connection and simulates the PIN entry on it. It bruteforces every possible passcode combination that is a 4-digit pin on the Apple device until it gets the correct one. What makes matters worse is that this method of violating an iOS device’s is capable of bypassing the “Erase data after 10 attempts” security feature. It does that by making a direct connection to iPhone’s power source and cutting the power after making a failed attempt. The device is able to cut the power before the device syncs the information about the failed attempt to the flash memory.
The iOS device used for this test was an iPhone 5s powered by iOS 8.1. While the trick of cutting the power lets hackers by pass the “Erase data after 10 attempts” security feature it also prolongs the process. According to MDSec trying each possible PIN combination takes up to 40 seconds, which means the whole process of unlocking the iOS device through the process of bruteforce could take up to 4 and half days (or less depending on how quickly it is able to find the code).
For now to protect yourself from this kind of breach you can use the complex passcode. To do so open Settings > Touch ID & Passcode > Turn off ‘Simple Passcode’. Then use a complex passcode containing numbers and letters. [MDSec]