Cybercriminals can compromise your iPhone and sensitive data with the help of hacking software that doesn’t require you to click on a link, according to the latest report from Amnesty International.
The resource revealed that discovered smartphones belonging to human rights lawyers and journalists had been infected with NSO Group’s Pegasus malware that allows hackers to access the iPhone’s camera, microphone, emails, and messages. It means that the organizations that use NSO Group software can compromise iPhones to spy on user data, using technologies unknown to Apple. Even if you regularly update your phone, you cannot stop a dedicated attack that employs fancy spy software.
The report also suggests that even if you change your behavior and don’t click on phishing links you receive in emails or messages, you can still become a victim of NSO software. In the past, older Pegasus versions required you to click a malicious link to provide the criminals with access to your data. But now, the technology used to employ these attacks can compromise your phone, even without you clicking on unknown links.
NSO Group is an Israeli company that sells software to law enforcement and government agencies that use the harvested information to prevent terrorist acts or identify sex and drug traffickers. Amnesty International revealed that the NSO Group spy software has targeted over 50,000 phones. Also, it looks like the hackers also targeted Android services, but it isn’t known if they experienced the same issues as iPhones.
Jailbreaking is not a requirement for infecting iPhones
Some reports claimed that hackers could infect only jailbroken iOS devices in an effort to educate people about the potential risks they exposed themselves to when they don’t follow Apple’s recommendations. Apple does a great job at protecting its clients from most malicious cyber threats, but the truth is that hackers can infect even non-jailbroken devices with spyware.
Hacking Team, an Italian spyware provider, was hacked, leaving smartphone users vulnerable to cyberattacks from entities using its software. It looks like Hacking Team’s customers are looking for ways to compromise jailbroken iOS devices. For an extended period, Hacking Team possessed an Apple enterprise certificate that allowed apps signed with the certificate to be installed on iOS devices (both jailbroken or not). Hacking Team used the certificate to sign an app containing spyware and hide it in the Newsstand app, preventing iOS devices from finding it.
Apple created enterprise certificates to allow developers to create custom apps without needing Apple’s review. In theory, the enterprises can use the certificates to install the apps only on employee devices, but it looks like they can install the apps on any iOS device.
While Apple created security warnings to inform users they should carefully check the app’s nature before installing it outside the App Store. Sadly, it looks like people ignore these security warnings, especially when the app promises to fix one of their burning issues.
Apple users can get many apps from third-party sources, even on non-jailbroken phones if they are signed by developer or enterprise certificates. After they install and open the app, it’s fully functional even on non-jailbroken iPhones.
The Hacking Team used three methods to get spyware onto its iOS devices:
- The user clicked on a link to download from an email, message, or website
- There was a desktop app that appeared to do the same
- An OS X app sideloaded an iOS app automatically to a smartphone when it was plugged via USB.
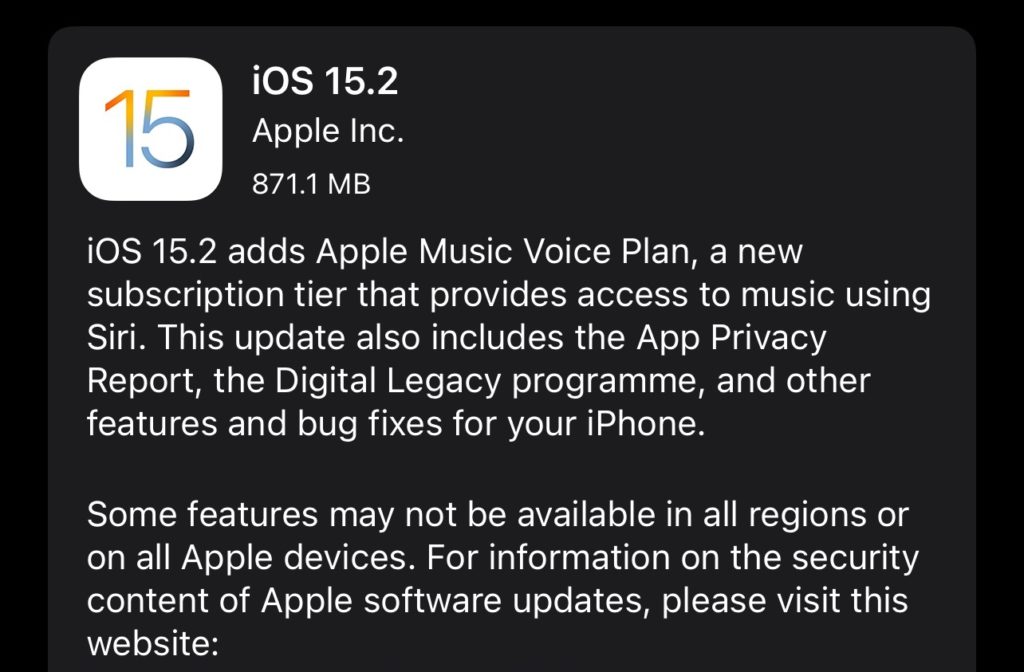
Software update can fix some security issues
Security experts suggest that the best way to stop malware from compromising Apple devices is to upgrade them with the latest software. However, to do it, Apple needs to continually check what malware attackers use and develop solutions able to stop it from hacking its devices. If there are still issues created by organizations like NSO Group or Hacking Team, Apple failed to fix the exploits. After it does it, its clients can protect themselves by updating their devices to the latest version of the operating system. This means that malicious software could lose its capabilities or stop working if Apple fixes the exploits immediately it finds about the attack.
Most cyberattacks are highly sophisticated, quite expensive, have a short shelf life, and target specific individuals or organizations. While it may mean they don’t target all users, Apple should continue to work tirelessly to defend all its clients and add new layers of protection for its data and devices.
The most common types of iPhone hacks
Hacking usually occurs when someone gains access to personal data on your iPhone device or controls it without your consent. Here is a list of the most common types of iPhone hacks.
Suspicious links or websites – similar to other devices, iPhones can be hacked if you click on a suspicious link or website. Don’t access a website or link if you think it feels off. Also, avoid connecting to password-free public Wi-Fi networks that allow hackers to access unencrypted traffic on your devices or redirect you to fraudulent websites.
Suspicious apps on the App Store – Apple devices exist in a monitored and closed ecosystem, but even if the company has a vetting process for the apps in its store, it’s not bullet-proofed, as shown above with the Hacking Team apps. Cybersecurity professionals state that you should always watch out for apps that ask for more information than they need to function.
Targeted attacks – if you’re an average individual, you probably won’t be singled out and targeted by hackers because it’s expensive to employ an attack. Activists and journalists are most at risk for cybersecurity attacks. Criminals usually exploit unknown flaws in the iOS programming that even the developers missed. They install malware to harvest information from targeted sources. These bugs are named zero-day exploits because Apple finds about its security issues the same day the hackers patch it.
Cybersecurity specialists state that NSO Group software doesn’t stay on devices when rebooted, so it’s challenging to say how many devices were infected.