Apple Macs were recently hit with a type of malware that is commonly known as Ransomware. The news came as a shock to Mac users, who unlike Windows users are not used to of anticipating a malware outbreak on their computers. Mac Ransomware is something that every OS X user should worry about and take steps in order to prevent it from affecting their computers. If you are not familiar with what Mac Ransomware is and how you can protect yourself from it, then you have come to the right place. In this article we will tell you what exactly Mac KeRanger Ransomware is and how you can protect your Mac from it.
What is Mac Ransomware?
Before we start talking about ways to protect your Mac from Ransomware, it is important that you understand what Ransomware is. The Ransomware is a type of malware for computers that restricts the user from having access to his or her computer. It kind of holds user’s data or access to the computer as ‘hostage’ until the user pay a ransom, hence the name ‘Ransomware’. The hackers who orchestrate the hack remove the restriction once the affected user has paid the demanded money. Hackers use different techniques to restrict access to a computer, most notably they would encrypt files on user’s hardware, making it impossible for the user to decrypt the data stored in it without the encryption key held by the hacker.
How did the Macs got affected?
Recently the popular Mac Bit-Torrent app Transmission received an update after nearly two years. The KeRanger Ransomware was stored in the version 2.90 of the application. When users updated to the new application version, the Trojan malware came into action and installed itself into the machine, effectively getting itself in the position of restricting user’s access to their Mac. The Transmission 2.90 update was pushed on 4th March, and the malware started affecting machines 3 days after it was first installed. Once active KeRanger encrypts files stored on user’s hard drive and asks for 1 bitcoin or roughly $400 to decrypt the system.
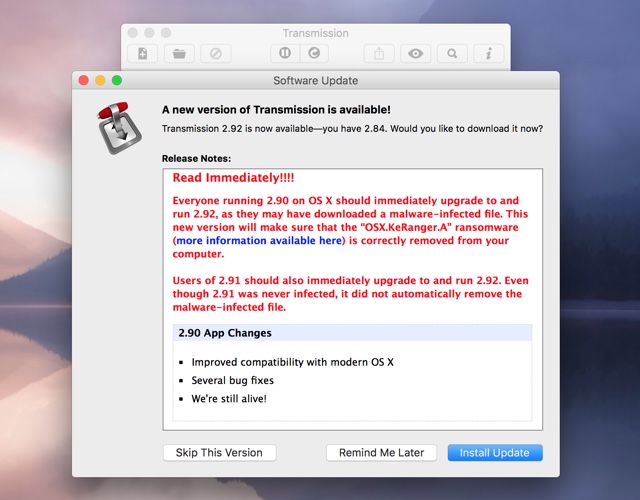
Since the first release of the Trojan laden Transmission 2.90, the original developers of the open source Bittorrent client have pulled the affected version and have pushed 2.92, which not only removes the malware from the app itself but also from user’s computer.
How to remove KeRanger Mac Ransomware?
After the malware was detected developers of Transmission have pushed version 2.92, which removes any traces of this Ransomware. Apple has also revoked the GateKeeper certificates that the hackers took advantage of.
To update Transmission to the safe version 2.92 open the application, and from top menu bar go to Transmission > Check for Updates.
While everyone using the Transmission app should install the latest 2.92 version, it is especially recommended for those who downloaded the update 2.90 between March 4th 11:00 A.M. PST and March 5th 7:00 P.M. PST.
You can also follow the steps shared by Palo Alto Networks that will help you in finding whether your Mac is affected by this particular Ransomware and manually remove it.
1. Using either Terminal or Finder, check whether /Applications/Transmission.app/Contents/Resources/ General.rtf or /Volumes/Transmission/Transmission.app/Contents/Resources/ General.rtf exist. If any of these exist, the Transmission application is infected and we suggest deleting this version of Transmission.
2. Using “Activity Monitor” preinstalled in OS X, check whether any process named “kernel_service” is running. If so, double check the process, choose the “Open Files and Ports” and check whether there is a file name like “/Users/
/Library/kernel_service” (Figure 12). If so, the process is KeRanger’s main process. We suggest terminating it with “Quit -> Force Quit”. 3. After these steps, we also recommend users check whether the files “.kernel_pid”, “.kernel_time”, “.kernel_complete” or “kernel_service” existing in ~/Library directory. If so, you should delete them.