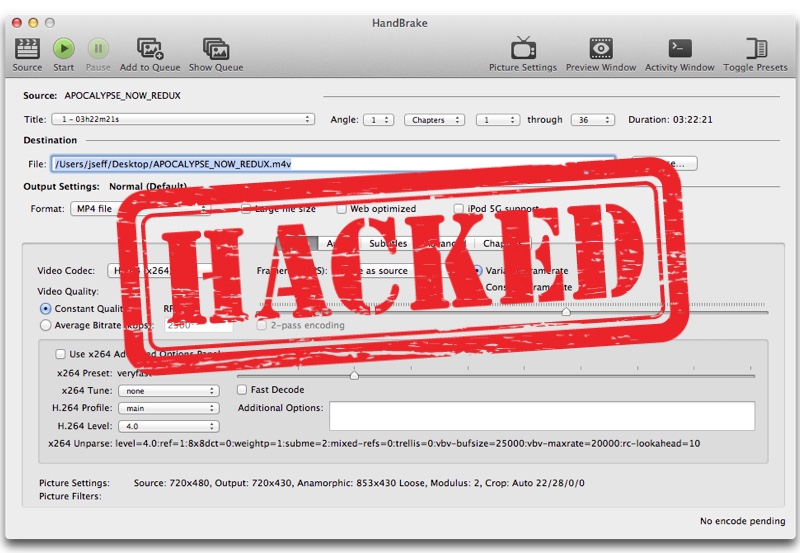
If you are a user of the popular HandBrake video transcoder app for Mac, then you might want to read on. The developers of the desktop app have revealed that one of the mirror download links for the HandBrake app was compromised between May 2 and May 6. Any downloads that occurred during this time were served a compromised version of the HandBrake-1.0.7.dmg, which contains a trojan virus capable of providing root access to intruders.
According to the developers hackers targeted download.handbrake.fr mirror and replaced the download file on this server with a malicious file. They note that there is a 50/50 chance of a user’s computer who downloaded the app between May 2 and May 6 getting affected by the malware. If you did not download the HandBrake app during this timeframe, then you are safe. However if you did or you are not sure about the exact date but have downloaded HandBrake recently, you can check if your machine is infected.
Those who upgraded to HandBrake 1.0.7 from version 1.0 are not affected, however users who were running HandBrake version 0.10.5 or earlier and upgraded using the built-in updater might also be at risk.
To check simply open the Activity Monitor app on your Mac and check for ‘Activity_agent’. If this process is running, then it means your Mac is infected by the trojan. On the HandBrake forums there are also advises for users affected by the hack. Users can run certain Terminal commands to get rid of the virus.
Users are also advised to change the passwords in the OSX KeyChain as well as those that are stored in the web browser to avoid their accounts getting hacked.
This particular malware is called OSX/Proton.A, which allows hackers to perform keystroke logging, file downloads and uploads, accessing webcam to take photos, take screenshots and have SSH and VNC connectivity on the infected machine. (AppleInsider)