According to Apple it has fixed a zero-day vulnerability with iOS 16.1. The company says the exploit may have been in active use, making it crucial for users to upgrade their devices to iOS 16.1 as soon as possible.
The zero-day vulnerability that has been fixed in iOS 16.1 is a kernel exploit, which means it has the potential of allowing hackers to run malicious code on targeted device.
The kernel level exploit affects all modern models of iOS devices that are capable of running iOS 16. This includes iPhone 8 or later.
For those unaware, Zero-Day vulnerabilities are those exploits that are known to hackers before they become known to the company itself. These vulnerabilities are dangerous because they can be exploited in the wild before a company is able to push a fix. As noted earlier Apple believes the vulnerability CVE-2022-42827 might also have been exploited in the wild.
Here’s how Apple has described the vulnerability on its Security content website.
Available for: iPhone 8 and later, iPad Pro (all models), iPad Air 3rd generation and later, iPad 5th generation and later, iPad mini 5th generation and later
Impact: An application may be able to execute arbitrary code with kernel privileges. Apple is aware of a report that this issue may have been actively exploited.
Description: An out-of-bounds write issue was addressed with improved bounds checking.
CVE-2022-42827: an anonymous researcher
While such vulnerabilities are usually exploited by hackers and nation states to target high profile targets, they are also used by jailbreak developers to jailbreak iOS devices and open their software up for modifications that are not allowed by Apple.
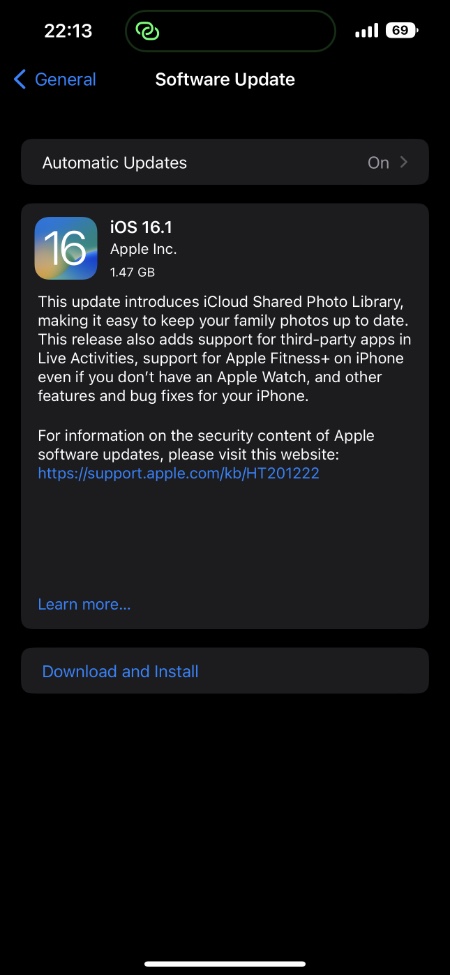
If you are someone who has yet to update his or her device to iOS 16.1, then it is advisable that you do so by going to Settings -> General -> Software Update.