Almost every business today has an online presence or uses computer systems to run various applications and processes. Although technology made it easier to run businesses efficiently and smoothly, it opened up a whole new level of security threats.
The past decade alone has seen thousands of data breaches reported all over the globe, putting business owners on high alert for cyber breaches. A cyber breach puts the victim’s consumer trust, network integrity, and reputation at risk, a reason entrepreneurs, should take a proactive approach to keep their systems safe and secure.
Discussed below is a list of 9 essential cyber security measures and tips businesses can implement to protect themselves from cyber-related attacks.
1. Create A Security Approach
The first step to keeping your business secure is having a system to help review, manage, and address the various security needs. You can achieve this by:
a. Setting A Budget
You need a budget plan in place for maintaining security. Proper budgeting is therefore required for all the needed security products, software solutions, and human resources. While these measures may seem expensive at first, the cost doesn’t compare to what you’d pay in the case of a data breach.
It will be easier to monitor, evaluate, or even revamp security as required with a dedicated budget in place. A huge budget doesn’t necessarily translate to better security coverage. You thus don’t have to spend more than you have, but just enough for cyber security.
b. Hire A Dedicated Security Professional
You need to have at least one in-house cyber security expert to help monitor and manage your security systems. While hiring third-party security providers might seem like a better option, you need to have someone that understands the specifics of your business operations.
An in-house IT expert can help identify security flaws and patch them before the worst happens, and even counter an imminent attack before the outsourced experts can come in.
c. Ensure Everything Is Up-To-Date
The computer security industry is constantly evolving with newer, more advanced systems developed to help with ever-advancing and newer cyber threats. An equipment/security software that was efficient a few years ago might not be as effective today, a reason you should evolve with time.
Keeping your software systems up to date (enabling automatic updates) and switching to newer, more robust security equipment can help wade off security threats. An in-house IT and security expert can help ensure all systems are updated and address any security vulnerabilities.
2. Know and Address Potential Key Threats
You need to have at least an idea of the various threats relevant to your business, to formulate a solid plan to prevent and protect yourself from the same. After identifying the threats, you can take the necessary measures to improve security and inform your workforce on how to stay protected. The most common vulnerabilities that SMEs have to watch out for include:
i. Email Security Threats
Most hackers use spoofing emails to target and gain access to digital business ecosystems. With many businesses using emails as a preferred communication method, hackers can trick unsuspecting employees into clicking a link or downloading an attachment with malicious code, infecting their computers and network systems.
Make sure your employees are accountable for their email security by arranging workshops and training programs. They also need to understand how cybercriminals think and avoid using anything that could make them potential targets, such as unsecured connections, public Wi-Fi, or unauthorized devices.
ii. Phishing Scams
A hacker can send you an infected email pretending to be someone you know or trust and trick you into sharing private and confidential information. They primarily achieve this by asking you to click on a link that redirects you into a login portal (for example) quite similar to what you know.
Entering your login details on the portal grants the hacker your privileges, a reason everyone needs to be careful when dealing with such. One way to prevent and avoid phishing scams is to have an email-screening service in place and sensitize them on ways to handle unsolicited and suspicious emails.
Having email security software (for pre-screening emails) in place can also help lower the risk of phishing attacks.
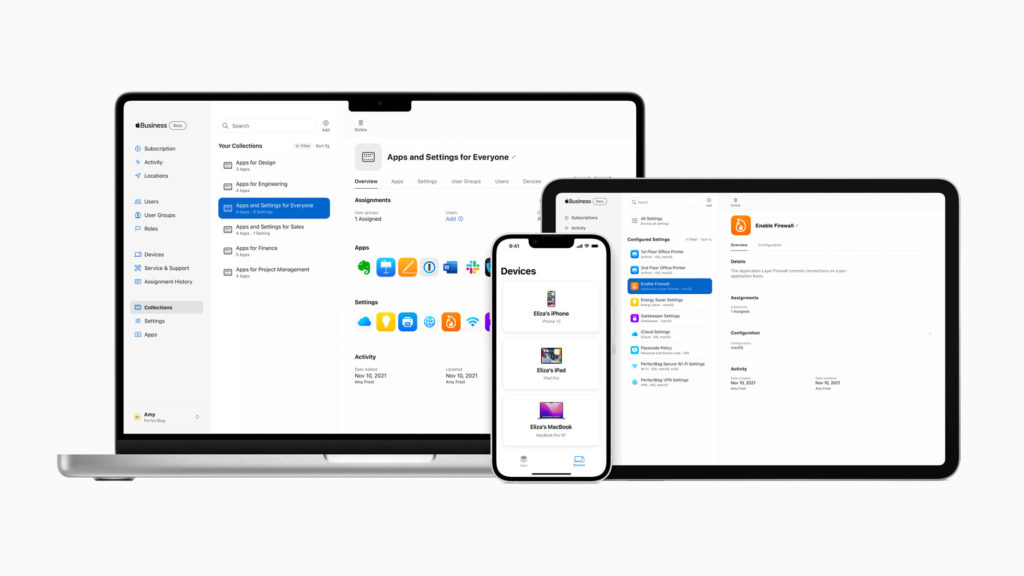
3. Use Integrated Products and Solutions
Avoid using security products and software that aren’t compatible with each other. Attempting to use incompatible systems will only leave you exposed to malware and data breaches. That being said, it would be advisable to invest in security components that can be integrated to form one robust security system. This includes everything from firewall systems, malware protection apps, email security software, and physical cameras, among many others. Integrated systems offer better protection than several pieces working individually.
Always go for systems compatible with your current setup when upgrading or installing new security features. Consider going for security systems your IT team is conversant with and those they can manage effectively without second-guessing themselves. Arrange for training workshops if additional training is required to run and manage the newer systems. Embrace system automation, where possible, to enable the IT personnel to focus on more valuable and pressing tasks.
4. Always Go for Authorized Solutions
In other words, only use enterprise-grade solutions for all your cyber security needs. Find out more about the future of security solutions and XDR. While it might be tempting to purchase an anti-virus, firewall, or other products from a third party at ‘irresistible’ discounts, chances are the products aren’t genuine or tampered with.
Always check with the original supplier to see if the vendor is authorized before buying such products. While the products may seem or work almost the same way as the ‘real deal, it is best to deal with the original supplier for authenticity and peace of mind.
Going for substandard or cheap products will only be putting your business at a significant security risk. Some of these solutions, especially pirated content, may contain malware or viruses designed to steal or corrupt valuable data. In addition to this, using the backdoor also means you won’t get proper customer support when the need arises.
5. Reinforce Your Security Awareness
In addition to having relevant security frameworks and structures in place, you still need to stay up-to-date on security awareness. One way to do this is to implement standard monitoring and approval procedures for all practices.
6. Schedule Regular Security Inventory Checks
The IT department is one of the busiest in most small and medium enterprises. The IT experts are always on the lookout for immediate security updates or busy upgrading, modifying, or monitoring the current infrastructure. This leaves them with less time to run security checks and inspections regularly.
Consider scheduling regular inventory security checks at least once every six months to ensure everything is in check. It’s through these checks that you’ll be able to identify and discover gaps within your security systems as well as the IT team in general. Identifying such loopholes on time makes it easier to fix before a hacker sees and seizes the opportunity.
This can be anything from technical certifications and recent training to participation in the latest security conference and training.







