When checkm8 exploit was made public everyone rejoiced because it opened new prospects for lifetime jailbreaks for certain devices. In fact it wasn’t long after the exploit was made public that we saw the release of checkra1n iOS 13 jailbreak.
Now it looks like iPhone the checkm8 exploit’s usefulness to hackers goes beyond jailbreaks, as Elcomsoft, a company that sells iPhone unlocking tools to law enforcement agencies is claiming to have the ability to extract user data from locked devices. The company says it is able to extract sensitive user data from devices running iOS 7 all the way up to the latest iOS 13.3 update by taking advantage of the checkm8 exploit.
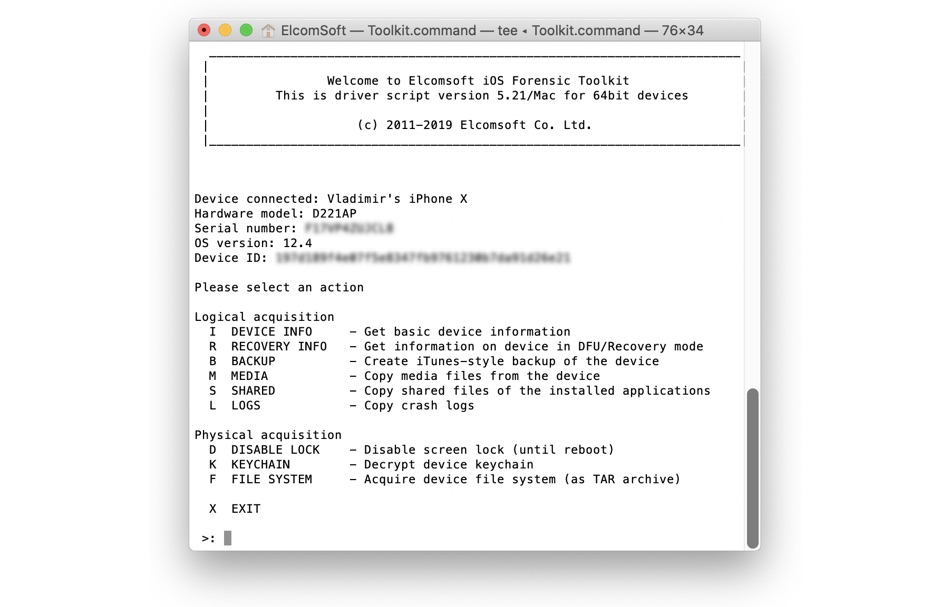
According to Elcomsoft, its $1495 iOS Forensic ToolKit works on all iPhones that are affected by the checkm8 exploits, which includes iPhone X and all iPhone models released before it. The company claims its tool can extract user’s data from locked iPhones even when the device in its BFU or Before First Unlock state. The tool also works after the iPhone has been rebooted. In addition to iPhones this exploit can also be used on iPads that have A11 chip or lower.
While Elcomsoft’s tool is not able to unlock the full device, it is however able to extract at least some data from the device. This includes data stored in the iPhone’s keychain such as credentials for the email accounts.
For the tool to be able to extract user data on a locked device, it needs to be jailbroken first. However Elcomsoft notes that jailbreak can be installed via DFU mode using the checkra1n jailbreak tool.
Millions of devices are affected by this hack and are vulnerable to Elcomsoft’s tool. However good news is the tool only works on devices that are vulnerable to checkm8 exploit. So newer iPhone models that were released after iPhone X, which includes iPhone XS, iPhone XS Max, iPhone XR and newest models such as iPhone 11, iPhone 11 Pro and iPhone 11 Pro Max are safe from this hack.







